Goal
In multi tier architecure design, we are placing our databases in a private subnet with no public IP and web-servers in public subnet which can have public IP. The Idea here is only the front end web-servers will be able to communicate with the backend servers, and backend servers cannot be directly accessed by outside world. But in some cases we may need internet access on private subnet machines for updating/installing softwares, patches etc. Here I will show you how to achieve this goal by using a NAT instance in OCI.
What we are going to do?
Our plan is to configure a Linux box in public subnet as a router (NAT - Network Address Translation). All the machines in the private subnet to initiate outbound IPv4 traffic to the internet at the same time those instances are prevent from receiving inbound traffic initiated by someone on the internet. The route table for those machines in private subnet will be the nat instance IP.
Architecture
Assumption
- You have an OCI account with needed permissions to create instance, network components.
- You already have a compartment to work on.
Follow the steps to reach our goal
Create VCN and Internet Gateway
Create a VCN with CIDR block value will be 10.0.0.0/16
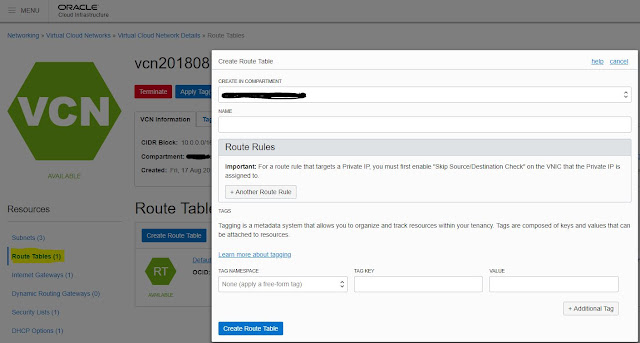
Create Public and Private Route tables
Create Private and Public Security Rules
We can add rules later for each security list, let it be clean now
Create Private and Public Subnet
Private subnet maps to CIDR Block 10.0.0.0/24 , Private Route Table, Private Security List and Public subnet maps to CIDR Block 10.0.10.0/24 , Public Route Table, Public Security List
Edit Public and Private Security List to allow the following IP and protocol
Ingres Rules for Public Subnet
- Allow SSH from anywhere 0.0.0.0/0
- Allow Ping ICMP from hosts in the Private Subnet 10.0.0.0/24
- Allow TCP from hosts in the Private Subnet 10.0.0.0/24
- Allow Ping ICMP from hosts in the Private Subnet 10.0.0.0/24
- Allow TCP from hosts in the Private Subnet 10.0.0.0/24
Egress Rules for Public Subnet
- Allow outgoing All Protocols to go out Everywhere 0.0.0.0/0
Ingres Rules for Private Subnet
Ingres Rules for Private Subnet
- Allow SSH from 10.0.10.24
Egress Rules for Private Subnet
-Allow Outgoing all protocols to everywhere 0.0.0.0/0
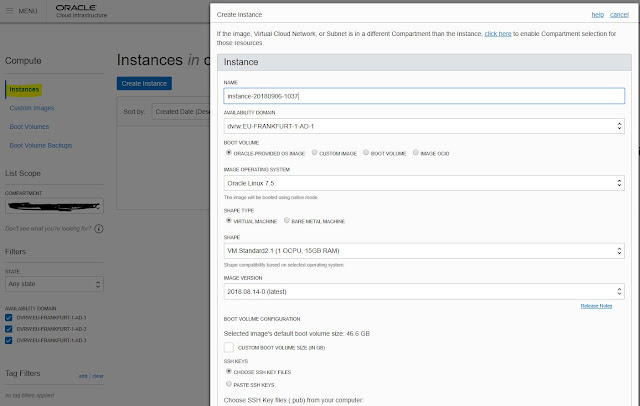
Create backend Server , Attach it to Private Subnet
Create NAT Instance , Attach it to Public Subnet
VNIC Configurations under Public Subnet
On NAT instance, edit the VNIC for to enable "Skip Source and Destination check"
Add one more Private IP Address 10.0.10.20 and Select NO Public IP
SSH to Public IP of NAT Instance
Login to the public server and upload your private ssh key to login to the private subnet server. Confirm whether you can SSH to private server from the public server
vi /etc/sysctl.d/98-ip-forward.conf
net.ipv4.ip_forward = 1
Save the file.
Run firewall commands to enable masquerading and port forwarding
firewall-offline-cmd --direct --add-rule ipv4 nat POSTROUTING 0 -o ens3 -j MASQUERADE
firewall-offline-cmd --direct --add-rule ipv4 filter FORWARD 0 -i ens3 -j ACCEPT
/bin/systemctl restart firewalld
sysctl -p /etc/sysctl.d/98-ip-forward.conf
Setting up NAT Address to all incoming traffic to NAT
This rule allows packets from the private subnet to route through the NAT instance (10.0.10.20)
Its the time to TEST
Login to your private server, see whether you can ping oracle.com or even curl/wget to oracle.com. Also you can see whether yum update works or not.
This means all the packets get routed to the NAT instance and from there it reaches to the internet gateway.
I am pretty much sure that you are thinking to automate this. No worries, we already have a Terraform scripts to automate the entire process. Want to know more, Click here












No comments:
Post a Comment